-
KanBo Installation
- KanBo Installation on Office 365 and Azure (Manual)
- KanBo Installation on Office 365 and Azure (KanBo Installer)
- KanBo On-Premises Installation Requirements and Prerequisites
- KanBo Installation On-Premise SharePoint 2013/2016/2019
- Creating and Updating the Elastic Cloud Deployment
- Creating a Linux Based Virtual Machine on Azure for Elastic Search
- Installing and Configuring Elastic Search on Debian
- Creating a Windows Virtual Machine on Azure for Elastic Search
- Installing and Configuring Elastic Search on Windows
- How to Create a X.509 High-Trust Certificate
- KanBo Setup
- KanBo Modern Webpart Installation
- Uninstall KanBo from Office 365
- Supported Browsers
-
KanBo Updates
-
Additional Components
- Setting Up KanBo Email Notifications on Azure
- Setting Up KanBo Email Notifications (On-Premise)
- KanBo Outlook Add-in Installation (O365 & On-Premise)
- Send Email to KanBo - Installation (Cloud)
- Send Email to KanBo - Installation (On-Premise)
- Enabling Email a Card Message
- KanBo and Microsoft Power Automate integration: Installation
- KanBo and Microsoft Power Automate Integration: Activation
- Configuring Power Automate with Your KanBo
- Installation of KanBo MyBoard Synchronization with Outlook Calendar and Outlook Tasks
- Installation of the Autodesk BIM Plugin for KanBo
- KanBo and UiPath Integration: Configuration
- Nintex Integration Installation
- KanBo API for Developers
- KanBo External User Groups (Active Directory Integration)
- KanBo Mini Application Installation
- Plugin for Adding Users to KanBo / Sharepoint When They First Enter it
- SharePoint Profiles Synchronization
- SharePoint Site Collection Balancing and Admin Warnings
- Sync Targets
- Installation of the KanBo Teams App
- Show all articles ( 1 ) Collapse Articles
-
Tips & Tricks
- Configure How Documents Should Be Opened from KanBo
- Customize KanBo Background Images and KanBo Colors
- Define Board Features to Be Enabled or Disabled by Default
- Disable Sleeping Tabs in Browsers
- Disable/Enable Public Boards Creation
- Find Out the Certificate Expiration Dates On-Premise
- Get KanBo ID
- How to Change the Help URL in Your KanBo
- Import Users to KanBo
- Renew Certificate for KanBo Graph Installation
- Show KanBo Version
- Removing syncing of profile pictures in the Profile Sync job
-
Troubleshooting
Renew High Trust Certificate
Following article describes steps needed to register new self-signed certificate used for the communication between KanBo and SharePoint (High trust certificate). Please follow these instructions in case your old self-signed certificate expired.
Step 1
Generate a new self-signed certificate.
Go to the IIS Server Manager, click on your server and choose Server Certificates. From the menu on the right side choose “Create self-signed certificate”, pick a name for your certificate and follow the next steps to create it. After the certificate has been created save it to a file by following these steps:
- Select -> Click on “Export” -> Follow the steps to save it as a .pfx file in a chosen location (we will use the location later when configuring the app)
- Select -> Click on “View” -> Details -> Copy to file -> Save it as a .cer file in the same location as the .pfx file
- Install certificate to LocalMachine store (DoubleClick it). Ensure certificate exist under Personal tree using Manage computer certificates (certlm).
Step 2
In order to remove the old certificate, launch SharePoint Management Shell. Please replace the parts in {} with your data and respect order of performing the commands.
Get-SPTrustedRootAuthority
Remove-SPTrustedRootAuthority -Identity {id of the KanBo high certificate form the results
from previous command}
Get-SPTrustedSecurityTokenIssuer
Remove-SPTrustedSecurityTokenIssuer -Identity {id of the KanBo high certificate
from previous command}
You can check it result in the Central Administration -> Security -> Manage High Trust
Step 3
Now you can register the certificate in SharePoint. Replace the parts in {} with your data.
$publicCertPath = "{the path to your self-signed certificate .cer file ex. c:\certs\cert.cer}"
$issuerID = "{Issuer ID from web.config}"
$authorityName = "{Your chosen authority name ex. KanBoServerAppsCerts}"
$certificate = Get-PfxCertificate $publicCertPath
New-SPTrustedRootAuthority -Name $authorityName -Certificate $certificate
$realm = Get-SPAuthenticationRealm
$fullIssuerIdentifier = $issuerId + '@' + $realm
New-SPTrustedSecurityTokenIssuer -Name $authorityName -Certificate $certificate -RegisteredIssuerName $fullIssuerIdentifier -IsTrustBroker
Iisreset
Step 4
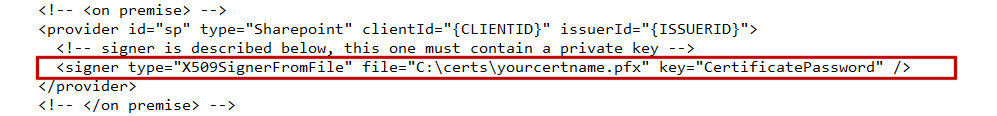
In case your organization is using a local certificate which is configured in the appSettings
instead of using the signer-attribute in the authentication-section, please perform the following change in the web.config file.
If your KanBo is older than 2.7.6, remove or comment entry with key="thumbprint" value="{Thumbprint}" store-name="my" store-location="localmachine" valid-only="false" /> and replace it with
<signer type="X509SignerFromFile" file="{C:\certs\yourcertname.pfx}" key="{CertificatePassword}" />
If your KanBo is newer than 2.7.6, remove or comment entry withkey="thumbprint" value="{Thumbprint}" store-name="my" store-location="localmachine" valid-only="false" /> and replace it with
<signer type="x509-file" file="{PathToPFXCert}" key="{PassForCert} />
You KanBo should start working good now.
